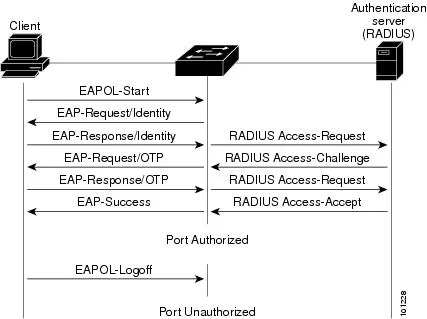
I/ 802.1X Port-based Network Access Control (PNAC) enables authentication of devices that connect to a local network. The below image illustrates the transmission of Extensible
Tag: Cyber security
Internal Network Attack Vector Discovery (Part II)
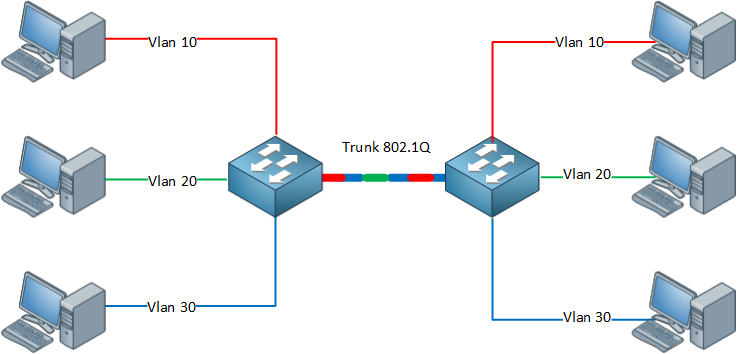
802.1Q VLAN VLANS are used within enterprises to segment networks and create individual broadcast domains. Along with reducing unnecessary broadcast of traffic, 802.1Q tagging limits
Internal Network Attack Vector Discovery (Part I)
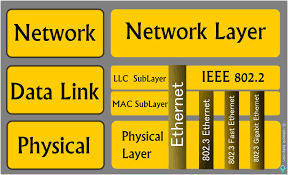
Most of the protocols using the data link layer and local broadcast addresses are nonroutable, which means you can only evaluate them from the local
TLS Security (Final) – Assessment
In this blog, we will go over some of the methods and tools to assess the TLS security posture during an engagement. Please remember to
TLS Security (Part II)
I. Understanding TLS Vulnerabilities Hackers can exploit some TLS flaws remotely, but practical exploitation of many requires network access to compromise ciphertext and data injection.
TLS Security (Part I)
I. What is TLS? Before getting into TLS security, let’s first talk about encryption. It can generally be applied at different levels, from encryption in
SECURITY FEATURES on MacOSX (Final)
We’ll go over the remaining security features on macOSX in this blog. 9. Firewall There is a built-in standalone firewall on MacOSX but it’s not
SECURITY FEATURES on MacOSX (Part I)
In this blog, we will go over some of the security features on MacOS that implemented by Apple to protect their users. Apple is known
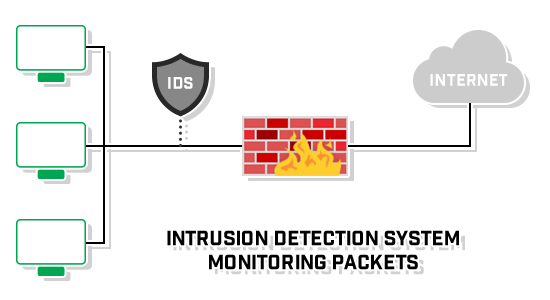
Introduction to IDS and IPS
An IDS or Intrusion Detection System monitors activity that is known or suspected to be malicious in its intent, raising alerts to a security or SOC teams to be analyzed.
IPS or Intrusion Prevention System adds another layer of defensive measure to protect resources.