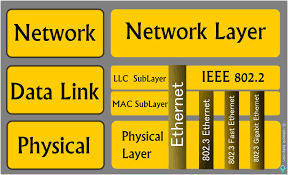
Most of the protocols using the data link layer and local broadcast addresses are nonroutable, which means you can only evaluate them from the local
Category: Pentesting
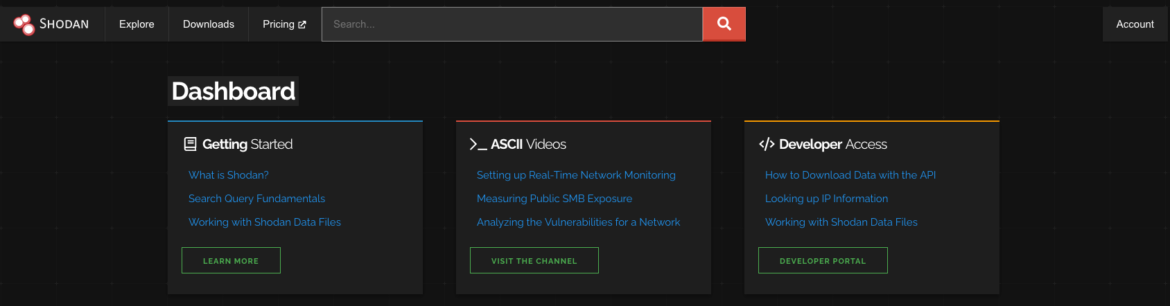
SHODAN For PENETRATION TESTER
In this blog, we will talk about how we can use one of the most commonly used search engines during the penetration testing process –
OSINT & Passive Recon
In this blog, we’ll look at what OSINT – Open Source Intelligence is and tools we can use to gather information about the target. Reconnaissance
How to Secure WordPress Part III
Let’s carry on where we left off last week (Part I and Part II). II. Secure Important Components 16. WordPress Security Keys & Salts WordPress
How to Secure WordPress Part II
Welcome to the next of the securing WordPress series. We’ll continue where we left off in part I. Secure WordPress Components (Contd) II. Secure Important
How to Secure WordPress Part I
I. Introduction When people talk about WordPress, often it would be something like: “it’s unsecured, it’s easy to get hacked,…”. But those are just misconceptions.
Common Network Attack Vectors
Today we are going to talk about a few common attack vectors, which are often taken when performing network penetration testing in enterprise and business